Provide Contractors,
Zero Trust Browser Isolation limits sensitive data leaks from unmanaged device use and protects users from threats when accessing high-risk web sites
Browser isolation enables organizations to extend Zero Trust principles to unmanaged devices to prevent data loss when accessing sensitive data and further reduces the risk of breaches from risky web destinations.
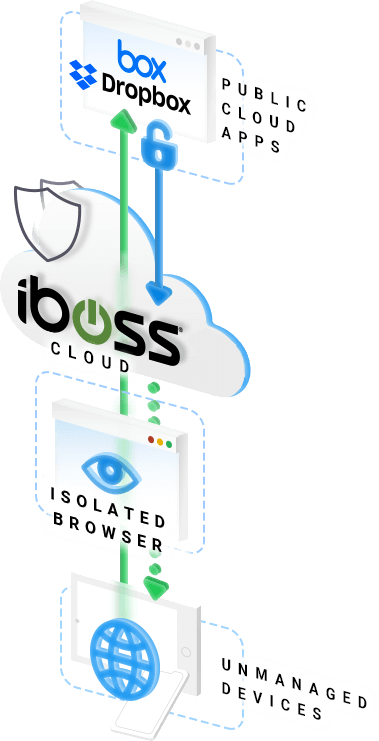
Isolate and secure unmanaged devices with Browser Isolation
Protect resources by securing enterprise application access for employees, contractors and third parties using unmanaged devices. For unmanaged devices, iboss Browser Isolation enables access to enterprise cloud applications without intrusive agent installs or the use of VDI. iboss Browser Isolation streams the protected content as pixels to the user’s browser, isolating the data from the unmanaged device. The browser isolation session prevents the user from downloading or moving data from an application to an untrusted location or device. This safeguards sensitive data and prevents unauthorized download by users on unmanaged devices.
Isolate resources and stop data leakage with Browser Isolation
Protect resources with browser isolation by providing read only access to employees and controlling upload and download activities to protect confidential information, even for users on enterprise-owned assets. iboss Browser Isolation enables productivity with fast access while limiting data leakage by controlling the ability to copy and paste data from the browser.
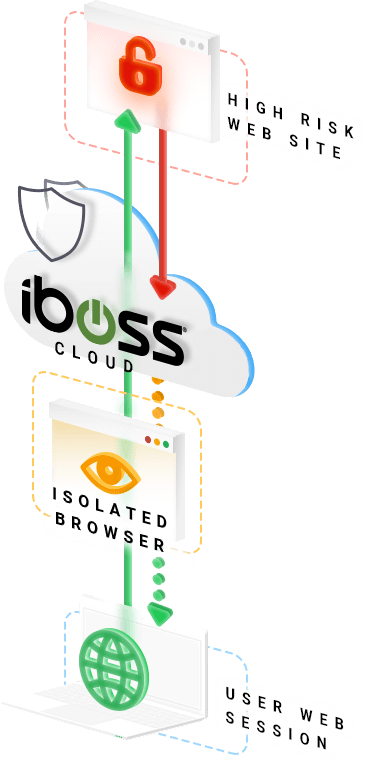
Isolate threats and protect against advanced malware with Browser Isolation
Enable a browser isolation session for cases where a user has requested access to a web site that has been categorized as high-risk. Instead of allowing the user to directly access the risky web site through their native browser, the iboss Zero Trust SASE will render the web content in an isolated browser session. The use of an isolated browser session ensures that the user’s browser and endpoint device never directly access the web content. The lack of direct access to content increases protection against malware and other threats.

Isolate and secure targeted employees with Browser Isolation
iboss Browser Isolation can be configured by policy for users or groups who are in departments or roles that are more likely to be targets of attackers, APTs or ransomware. In this use case, the iboss Zero Trust SASE can start a browser isolation session when the user is accessing sites hosting sensitive enterprise information. iboss’ pixel streaming ensures a fast, productive experience for those users.





