Read our Whitepaper on Positioning Your School District for Zero Trust
iboss is E-rate eligible
Download our free eBook

Overview
Secure your users’ internet access and school data on any device, from any location, in the cloud
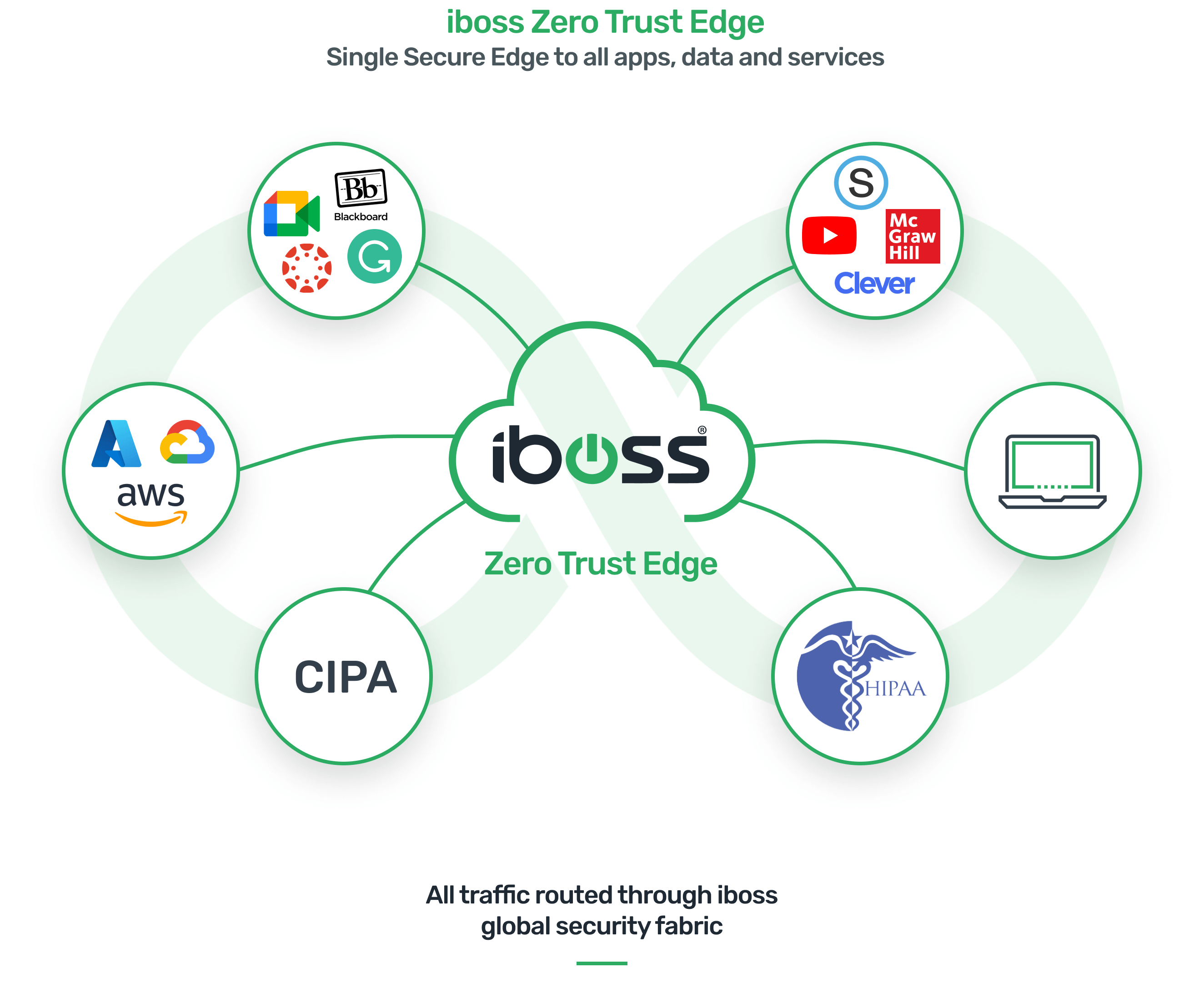
The iboss Zero Trust SASE provides CIPA compliant safe and secure Internet access for students and staff whenever they access the internet from school, home or wherever they may be while simultaneously protecting sensitive school data from cyberattacks including ransomware.
The iboss Zero Trust SASE delivers a next generation, military grade cloud based firewall platform that is E-Rate eligible. iboss enables schools to eliminate purchasing and managing multiple legacy technologies including Internet web filters, VPNs or the need to redirect student internet access to the school while they work from home.
This results in unmatched visibility and internet policy management across all students while increasing the school’s cybersecurity posture to military grade standards and protect the schools most critical data from cyber-attacks.
Seamlessly implement U.S. National Institute of Standards and Technology (NIST) recommendations to protect against cyberattacks
NIST is a physical sciences laboratory and non-regulatory agency of the United States Department of Commerce. In response to the unprecedented number of cyberattack against organizations, NIST published SP 800-207 which provides organizations with a systematic guideline for updating their network cybersecurity to a zero trust framework, also known as perimeterless security, that modernizes security in a world where users are accessing the internet remotely and address the inadequacies of traditional network defenses.
The zero trust security model is “never trust, always verify”. The iboss Zero Trust SASE platform was purpose built from the ground up leveraging one of the world’s largest proprietary security cloud architecture which was designed take all the guess work out of implementing NIST’s guidelines making it easy for schools to increase their cybersecurity posture and protect its users and resources from cyber-attacks.

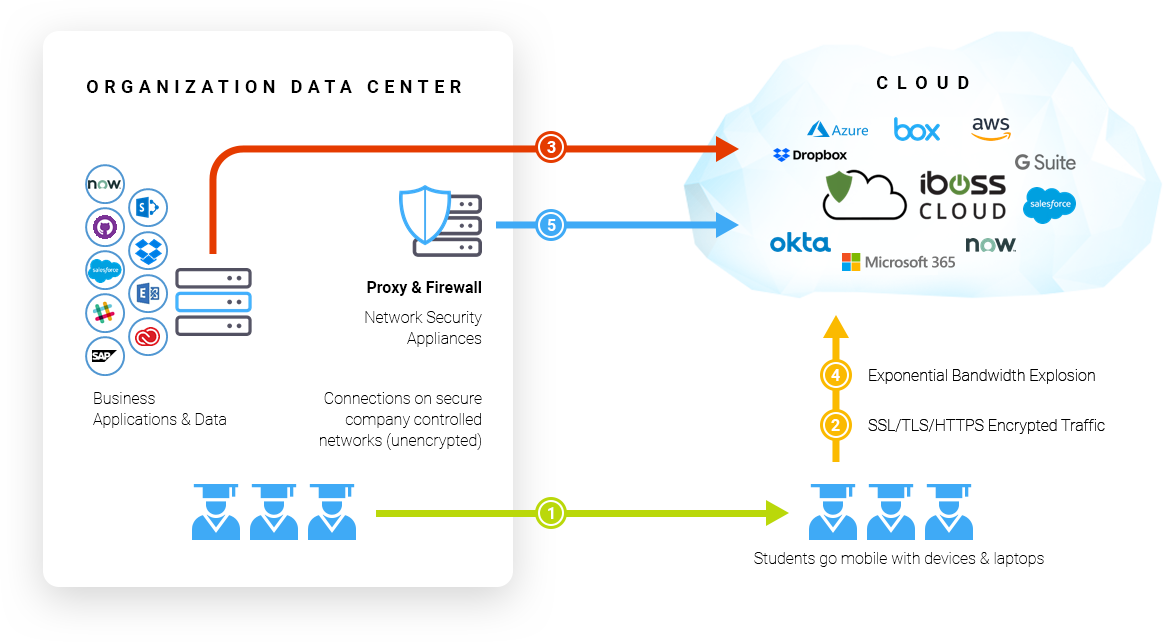
Your school’s sensitive data resides across various clouds and is accessed by staff from outside the network.
Legacy security architectures were based on a ‘castle and moat’ framework focused on restricting user access from outside the network.
This approach was effective because your school’s sensitive data (HR, Payroll, student health records, PII, etc.) resided on school owned servers hosted inside of school managed data center and accessed by users while on campus and on school managed devices.
Today, the vast majority of software is cloud hosted and being access by users and contractors remotely and on personal devices.
The result is your school’s sensitive data is now residing across multiple third party clouds and accessed from users who are not inside the ‘castle’ rendering traditional security ineffective in preventing cyberattacks. By shifting security to the cloud, iboss is able to reduce breach risk and protect your data where it resides, in the cloud.
Military grade zero trust security is essential to protect against social engineering attacks
Education is by far the top target for cyber attacks. From Aug. 14 to Sept.12, 2021, educational organizations were the target of over 5.8 million malware attacks, which represented 63% of all attacks. The preferred approach by cyber criminals is social engineering.
iboss Zero Trust SASE incorporates the next gen firewall tools which incorporate multiple attributes of a user when accessing cloud apps including the user’s physical location at the time of access, type of device they are accessing from, device security posture, user privileges and dynamically limits what can be accessed on the device based on these attributes.
This results in greater protection against ransomware, lower downtime for students and lowers the resources needed to manage security for the technology team.
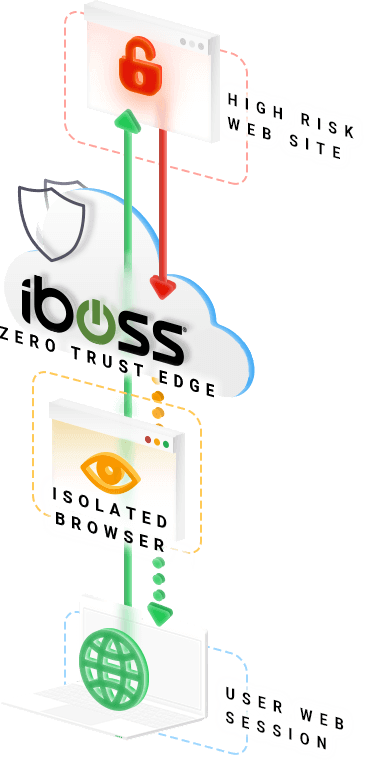
Browser Isolation provides unmatched protection against ransomware
In 2020, 77 ransomware attacks on U.S. schools and impacted 1.3 million students, resulted in 531 days of downtime at a cost of $6.6 billion in economic terms. Ransomware is a challenge for schools due to its unique dynamic with teachers, staff and administrators need to access files and web links as part of standard business operations. Unfortunately, it only takes one exposure to cripple the network.
iboss Zero Trust SASE incorporates Browser Isolation which allows users to access files and web links through a virtual pane of glass in the cloud decoupling the user from the actual files. If a file is malicious, the school’s network is completely isolated from the malicious content as the file never has the chance to touch the user’s device.
This results in massively lower exposure to ransomware, reduces student downtime due to a breach and potentially saves the school millions in losses from productivity, resources and paying ransoms.
Extends protection across all student devices regardless of location, including on campus and at home
High risk activity from at risk students isn’t always constrained to activity performed on campus. Since the iboss Zero Trust SASE follows the student to provide protection at all times, it has the ability to provide visibility to high risk activity while the student is off campus and at home.
This is critical in providing the visibility needed to prevent tragedies on campus and create the investigative reports necessary to deal with a high risk circumstance.
Provide students with a consistent, granular internet filtering policy whether they are on campus or at home regardless of device
With one to one initiatives, the goal is to assign one laptop to every child so that digital learning can continue at home. The challenge is that CIPA compliance must be met for all school owned devices regardless of location. With traditional web gateway appliances, filtering students while at home is challenging as the equipment for filtering typically resides on campus. With the iboss Zero Trust SASE, security follows the student, as it is delivered in the cloud. The school issued device is always connected to iboss and without the use of a VPN.
This ensures that the same level of protection and compliance is applied to a student regardless of whether they are on campus or at home. This also alleviates the challenges of securing devices by leveraging a cloud solution that can be deployed in minutes.
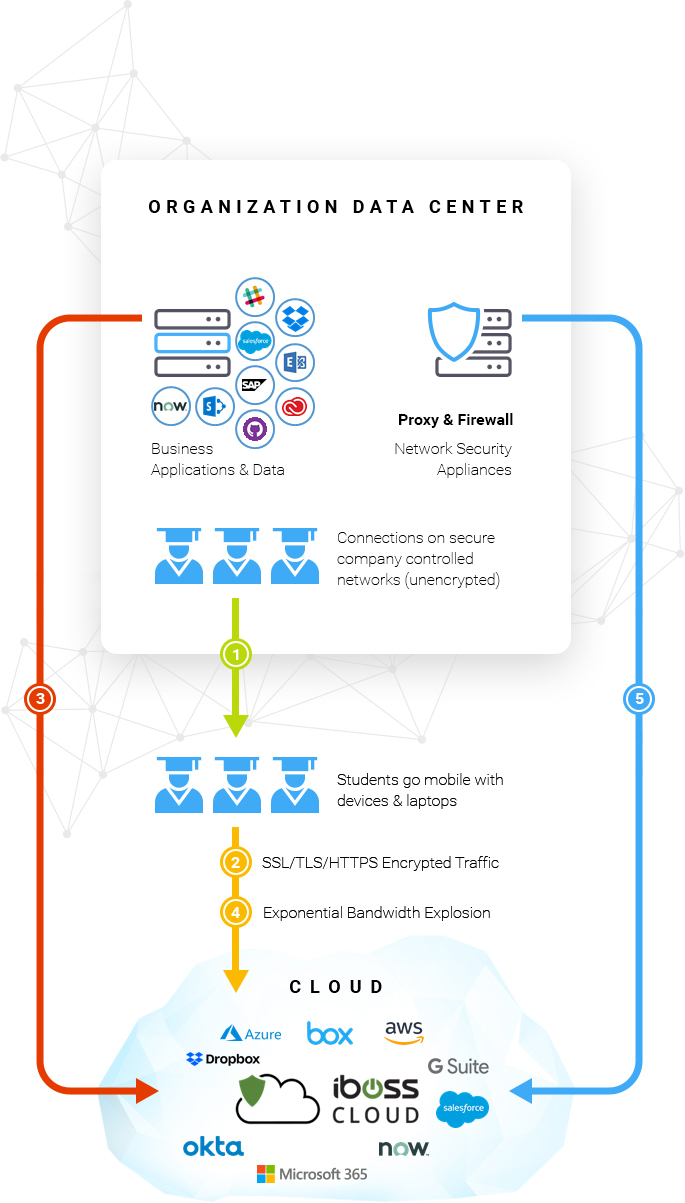
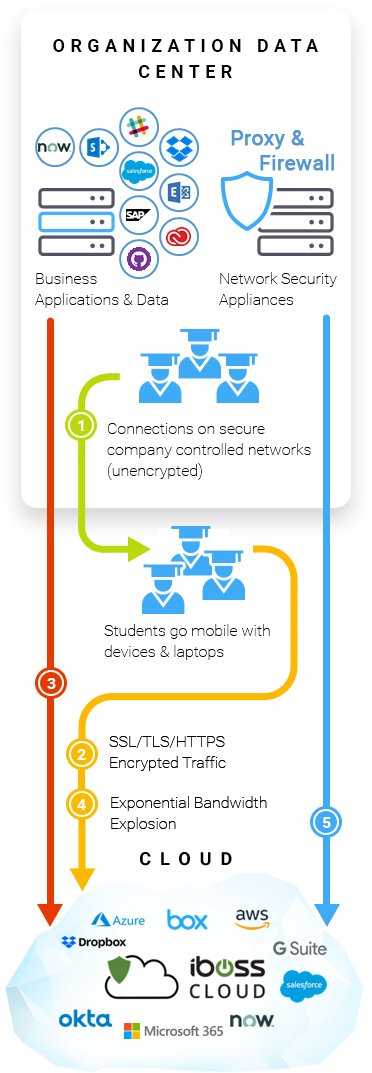
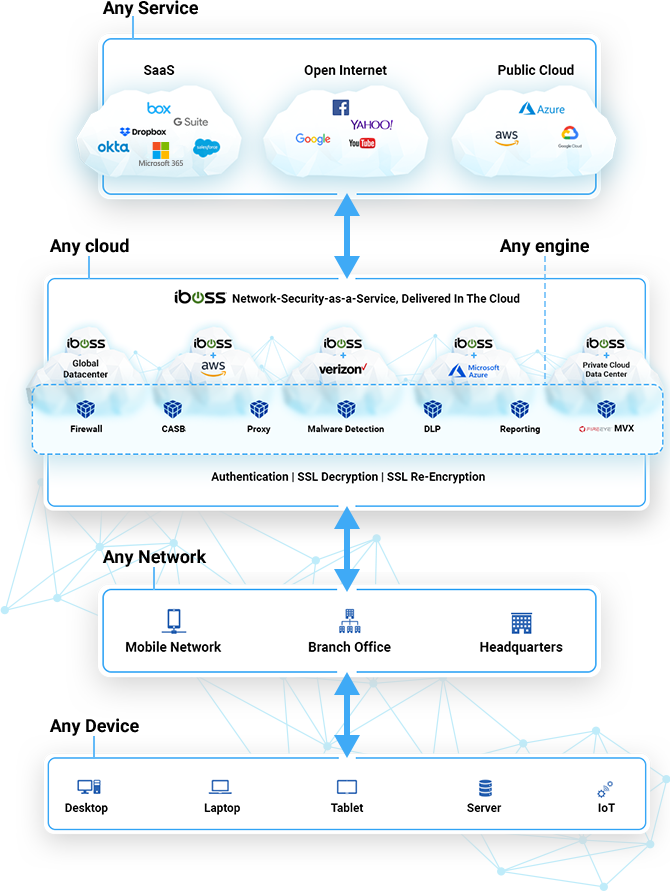
- Users Go Mobile
Desktops change to laptops and users are no longer in the network perimeter. - Encrypted Traffic
Unencrypted traffic shifts to encrypted HTTPS traffic due to mobility. - Cloud Applications and Files
Applications move from servers to SaaS, and data & files move to online storage & access. - Bandwidth Explosion
Increased bandwidth usage due to remote users accessing remote cloud data needed for productivity. - Security Moves to Cloud
Data Center network security moves to the cloud where the users, applications, and data live.
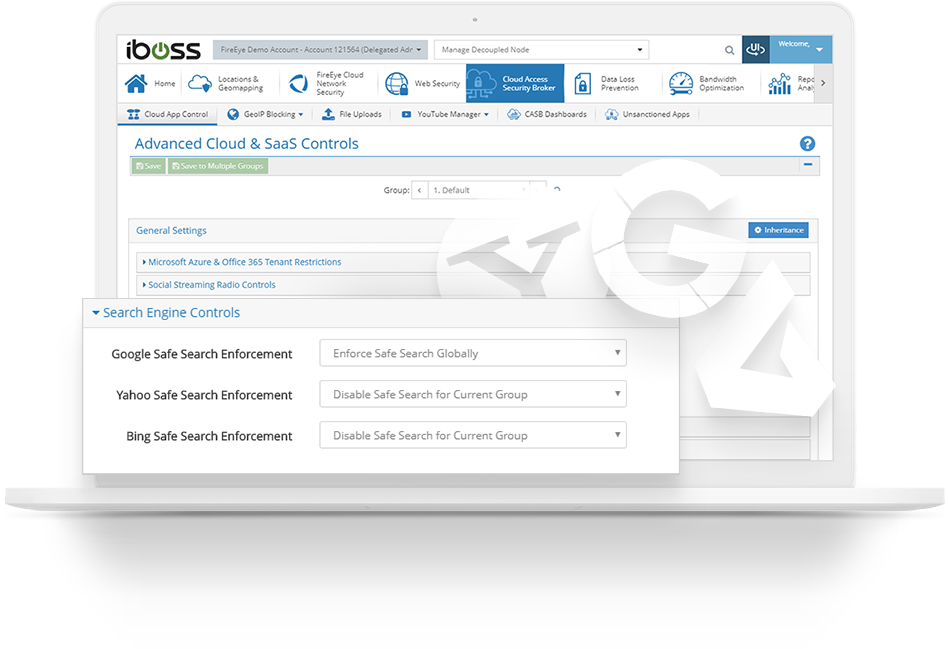
Enforce safe search on Google, Bing and Yahoo
Safe search can automatically be enabled and forced across popular search engines such as Google, Bing and Yahoo. The setting is enabled automatically and transparently to the user. In addition, enforcing safe search can be enabled on a per-group basis so that staff can have full access to search results when needed. Staff members can also override safe search results on-demand by creating override groups.

Fast and uninterrupted connections during testing season by leveraging the cloud
State testing has moved to the cloud. This means schools will need more bandwidth than ever as both testing and school classrooms are connected to the cloud at the same time. Testing content is becoming richer in nature and any slowdowns or interruptions lead to high stress IT departments. With iboss students can complete state testing with fast connections as data is secured in the cloud. This alleviates stress during this critical time so IT Administrators can focus their efforts on other critical areas.
This comparison matrix makes it easy to compare iboss’ features to those of your incumbent solution.
| Education Security Features | K12 Web Filtering Competitor | |
|---|---|---|
| Category Based Web Filtering to meet CIPA compliance |  |  |
| Secure Web Gateway with Proxy |  |  |
| Instant Messaging Application Controls |  |  |
| High Risk/At Risk Student Monitoring |  |  |
| Encrypted Traffic Inspection and Protection (HTTPS Decrypt) |  |  |
| Block Anonymizing Proxies |  |  |
| Protect Home Users without a VPN |  |  |
| Comprehensive Reporting down to the user level |  |  |
| Classroom Management |  |  |
| DNS Security |  |  |
| Reporting - including Real-Time Dashboards, Drill Down Reports, Reporting Templates |  |  |
| Cloud Connector Agents for Windows, Mac, iOS, Chromebooks, Linux and Android |  |  |
| Secure Access to Third Party Cloud Apps |  |  |
| Malware Prevention |  |  |
| Ransomware Detection and Prevention |  |  |
| Infected Device Detection and Isolation (CnC Callback Prevention) |  |  |
| Threat Dashboards |  |  |
| Phishing Prevention |  |  |
| Unified Zero Trust Service Edge |  |  |
| Zero Trust Resource Access Policies |  |  |
| Zero Trust NIST 800-207 Criteria-Based Access Policies |  |  |
| Asset Catalog |  |  |
| Asset and Device Posture Checks |  |  |
| Inline Data Loss Protection (PII, HIPAA, etc.) |  |  |
| Exact Data Match for DLP |  |  |
| Browser Isolation |  |  |
| Inline CASB |  |  |
| API CASB |  |  |
| SAML & OIDC Identity Provider (IdP) Integration |  |  |
| Log Forwarding to SIEM - Syslog, SCP, SFTP |  |  |

