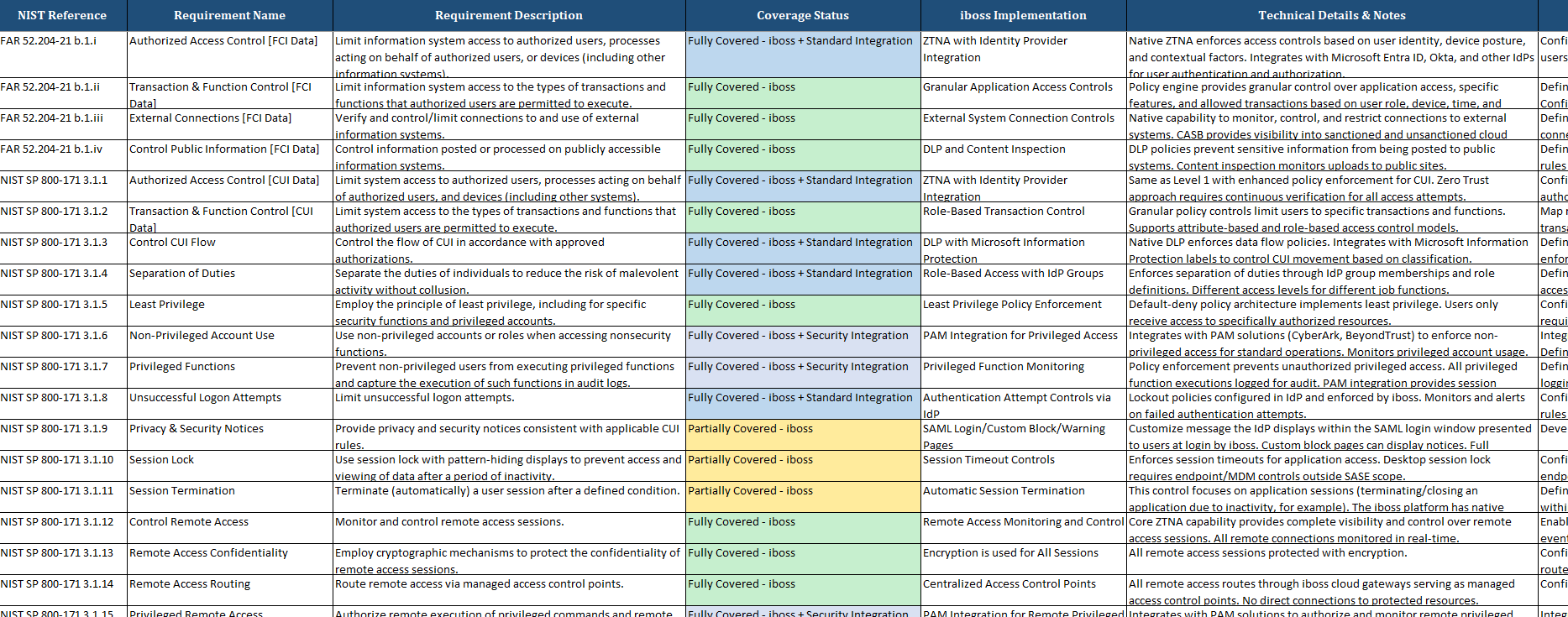
CMMC 2.0 Control Mapping Analysis
See exactly how the iboss SASE platform maps to all 125 CMMC controls across 14 security domains. Our comprehensive analysis shows 54% of controls fully covered through technology, with 100% coverage of all technology-applicable controls.
DoD Zero Trust Compliance Mapping Kit
Comprehensive technical assessment mapping the iboss SASE platform against all 152 DoD Zero Trust activities. Covers Target Level (FY27) focus with 61.5% of activities fully covered through technology and defensible coverage across all 7 pillars.
Government Security Certifications
iboss maintains the highest levels of government security certifications and compliance standards.
FedRAMP Authorized
Federal Risk and Authorization Management Program certification for government cloud services
Key Benefits:
StateRAMP Certified
State Risk and Authorization Management Program for state and local government
Key Benefits:
CJIS Compliant
Criminal Justice Information Services security policy compliance
Key Benefits:
Government Security Requirements
Meeting federal mandates and security frameworks with comprehensive Zero Trust capabilities.
Zero Trust Architecture
Executive Order 14028 mandates federal Zero Trust implementation
iboss Solution
Native Zero Trust SASE platform with identity-based access controls
Data Sovereignty
Government data must remain within authorized jurisdictions
iboss Solution
Geographically distributed cloud with data residency controls
Continuous Monitoring
Real-time security monitoring and incident response capabilities
iboss Solution
24/7 SOC with government-grade threat intelligence
Secure Communications
Encrypted communications for sensitive government operations
iboss Solution
TLS encrypted connections throughout, including end user connections and comprehensive logging
Government Use Cases
Real-world implementations across federal, state, and local government agencies.
Federal Agency Modernization
Challenge
Legacy IT infrastructure hampering digital transformation
Solution
Cloud-first Zero Trust architecture with secure application access
Key Outcomes
State & Local Government
Challenge
Limited cybersecurity resources and expertise
Solution
Managed SASE platform with automated threat protection
Key Outcomes
Law Enforcement
Challenge
Securing sensitive criminal justice information systems
Solution
CJIS-compliant platform with advanced access controls
Key Outcomes
Why Government Agencies Choose iboss
Mission-Critical Security
Purpose-built for government security requirements with continuous compliance monitoring.
Secure Employee Access
Zero Trust access controls for government employees accessing cloud applications and resources.
Automated Compliance
Built-in compliance controls reduce audit burden and ensure continuous regulatory adherence.