What is Zero Trust?
Understanding Zero Trust Architecture Per NIST SP 800-207
iboss Zero Trust SASE Platform
Purpose Built for Zero Trust to Protect Organizations from Breaches and Data Loss
The iboss Zero Trust SASE prevents breaches by making applications, data and services inaccessible to attackers while allowing trusted users to securely and directly connect to protected resources from anywhere
Applications, data and services have moved from the datacenter to the cloud, making them easily accessible by attackers. Users have left the office and are working from anywhere. Legacy security and visibility approaches rely on resources and users to be located in the office to provide protection which is no longer possible.
The iboss Zero Trust SASE is focused on protecting sensitive resources by making them completely inaccessible and invisible to attackers while strictly granting access to trusted and approved users from wherever they work.

NIST Risk Management Framework Applied To Zero Trust
Designed To Manage Risk Centered Around Effectiveness & Efficiencies
Greatly reducing cyber risk resulting in breaches and data loss is easily made possible using the iboss Zero Trust SASE because it tackles the problem from the various angles that make organizations vulnerable to attacks.
The platform provides the tools to follow processes outlined in the NIST Risk Management Framework which starts by understanding and classifying what resources exist and need to be protected.
"This definition focuses on the crux of the issue, which is the goal to prevent unauthorized access to data and services coupled with making the access control enforcement as granular as possible. That is, authorized and approved subjects … can access the data to the exclusion of all other subjects (i.e., attackers)."– Page 4, NIST SP 800-207

NIST Risk Management Framework
Zero Trust Basics
Core concepts of NIST 800-207 Zero Trust Architecture
Resource Access Control
Zero Trust is about resource access, not network access. Goal is to reduce risk of breaches and data loss by isolating resources with Policy Enforcement Points (PEP).
Per-Request Decisions
For each and every transaction, the PEP approves or denies the connection and logs the transaction. Policies based on "default deny" construct.
Complete Visibility
Provides key security and compliance controls: Access Control, Visibility via Logging, and Security (DLP, malware defense, compliance) for every transaction.
What is the difference between Authentication and Authorization?
Each request needs to go through both authentication and authorization
Use an "airport security checkpoint" as your basis for understanding NIST 800-207 Zero Trust Concepts
Authentication – Knowing who the person is
i.e. Check the traveler's ID before getting through the checkpoint
- • Identity verification process
- • Step-Up Authentication (Passport vs State ID)
- • Client Certificates (TSA Pre-Check)
Authorization – Giving the privilege to access the resources
i.e. Allow the traveler to pass the security checkpoint and board the plane (resource) only after security screening is completed
- • Resource access privileges
- • Security screening completion
- • Granular permission control
What is a Session?
According to NIST, a session is as granular as a single transaction between a user and a resource
- Understanding what a "session" means is VERY important
- A transaction is as granular as a SINGLE API call – a read followed by a write to a database consists of TWO transactions
- Each transaction ideally goes through authentication AND authorization
- This provides granular access control in addition to visibility (via logging) of every interaction
"The unit of "session" can be nebulous and differ depending on tools, architecture, etc. The basic definition in a zero trust context is a connection to one resource utilizing one network identity and one privilege for that identity (e.g. read, write, delete, etc.) or even a single operation (similar to an API call)."– Page 2, NIST – Planning for a Zero Trust Architecture
The Tenets of Zero Trust
Getting the Tenets right gives a solid foundation for Zero Trust to build on into the future
Tenet 1 – All enterprise-owned apps, services and data sources are considered resources, regardless of location
- This is one of the most critical tenets of Zero Trust to get right
- Do not think of Zero Trust as meaning access to on-prem resources (i.e. replacing your VPN)
- All resources regardless of type and location should be made private by putting them behind the Zero Trust service
- This includes on-prem, SaaS and Cloud (Azure, AWS) applications, data and services
Benefits Beyond VPN Replacement:
- Direct to resource access for employees wherever they work
- Access to resources within Azure and AWS
- Better productivity and end-user experience
- Reduced datacenter space requirements
Three Key Components: Subject, Asset and Resource
Resources Cannot Be Accessed Without Going Through The Policy Enforcement Point And Gaining Authorization
NIST SP 800-207 Zero Trust Framework
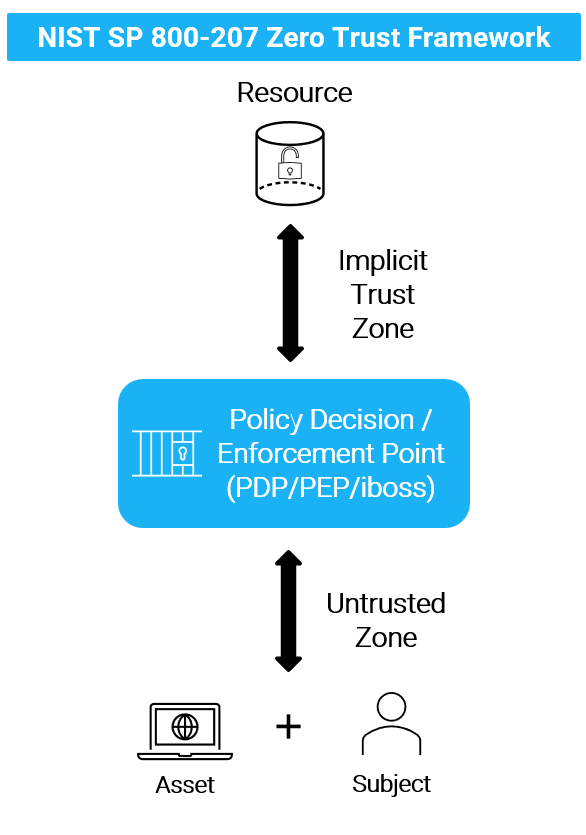
iboss Implementation Of NIST SP 800-207

Subject
This is typically the user. The term "subject" is used because this might be a non-human entity (service, AWS Lambda function, etc.)
Asset
This is typically a laptop, desktop or server. This can also be IoT or OT devices that need to be catalogued and managed.
Resource
This is an application, data or service that is being protected. Start with enterprise-owned resources that need protection.