CMMC Compliance with FedRAMP-Authorized Zero Trust SASE
Accelerate your CMMC 2.0 certification with iboss. Our FedRAMP Moderate Authorized platform provides the technical controls defense contractors need for NIST 800-171 compliance and CMMC Level 2 certification.
Run Your CMMC 2.0 Audit Online — Start in Minutes
The iboss CMMC Audit Platform is a purpose-built portal that walks you through CMMC 2.0 readiness, control by control. Map evidence to NIST 800-171, identify gaps, and produce assessor-ready documentation—without spreadsheets or guesswork.
- Guided assessments aligned to NIST 800-171 and CMMC Level 2
- Centralized evidence collection, gap tracking, and remediation status
- Multi-customer dashboard for primes, MSPs, and MSSPs
What is CMMC 2.0?
The Cybersecurity Maturity Model Certification (CMMC) is the Department of Defense's unified standard for protecting sensitive information across the defense industrial base. CMMC 2.0 requires defense contractors to implement and verify cybersecurity practices based on the sensitivity of the information they handle.
Unlike previous self-attestation requirements, CMMC mandates third-party verification through Certified Third-Party Assessment Organizations (C3PAOs), ensuring contractors actually implement the security controls they claim.
Compliance Deadline Approaching
CMMC requirements are appearing in DoD contracts throughout 2025. Contractors without certification risk losing contract eligibility. Start your compliance journey now—certification can take 12-18 months.
CMMC Implementation Timeline
CMMC Program Rule Effective
The CMMC 2.0 program rule became effective, establishing the certification framework
CMMC Requirements in Contracts
DoD begins including CMMC requirements in contract solicitations
Phased Implementation
CMMC requirements progressively appear in more DoD contracts over a 3-year rollout
Full Implementation
CMMC certification expected for all applicable DoD contracts
Understanding CMMC 2.0 Levels
CMMC 2.0 streamlines the original five levels into three, aligning directly with existing NIST frameworks
Foundational
17 Practices
Basic cyber hygiene practices for organizations handling Federal Contract Information (FCI)
Key Requirements:
- Basic access control
- Identification and authentication
- Media protection
- Physical protection
- System and communications protection
- System and information integrity
Who needs this: All contractors handling FCI
Advanced
110 Practices
Full alignment with NIST SP 800-171 for organizations handling Controlled Unclassified Information (CUI)
Key Requirements:
- All Level 1 requirements plus:
- Access control enhancements
- Audit and accountability
- Configuration management
- Incident response
- Risk assessment
- Security assessment
Who needs this: Contractors handling CUI
Expert
110+ NIST 800-172 Practices
Enhanced protection against Advanced Persistent Threats (APTs) based on NIST SP 800-172
Key Requirements:
- All Level 2 requirements plus:
- Enhanced security measures per NIST 800-172
- Government-led assessments required
- Applicable to highest-priority programs
- Additional APT-focused controls
Who needs this: Contractors with highest-sensitivity CUI on critical programs
How iboss Accelerates CMMC Compliance
Our FedRAMP Moderate Authorized platform provides pre-validated security controls that map directly to CMMC requirements
FedRAMP Moderate Authorization
iboss holds FedRAMP Moderate Authorization, meaning our cloud security platform has already passed rigorous federal security assessments. This provides a significant head start for your CMMC compliance journey.
NIST 800-171 Control Mapping
Our technical controls directly map to NIST SP 800-171 requirements, which form the foundation of CMMC Level 2 compliance. Leverage our pre-mapped controls to accelerate your assessment.
Audit-Ready Documentation
Generate comprehensive compliance reports with detailed evidence of security control implementation. Support your CMMC assessor with clear documentation of your security posture.
Continuous Monitoring
CMMC requires ongoing security monitoring. iboss provides 24/7 visibility into your security environment with real-time alerts and detailed logging for compliance evidence.
Cloud-Native Zero Trust
Meet Zero Trust requirements mandated by Executive Order 14028 and reinforced by CMMC. Our cloud-native architecture delivers identity-based access control everywhere.
Rapid Deployment
Defense contractors face tight CMMC deadlines. Our cloud-first approach enables rapid deployment without hardware procurement delays—get protected in days, not months.
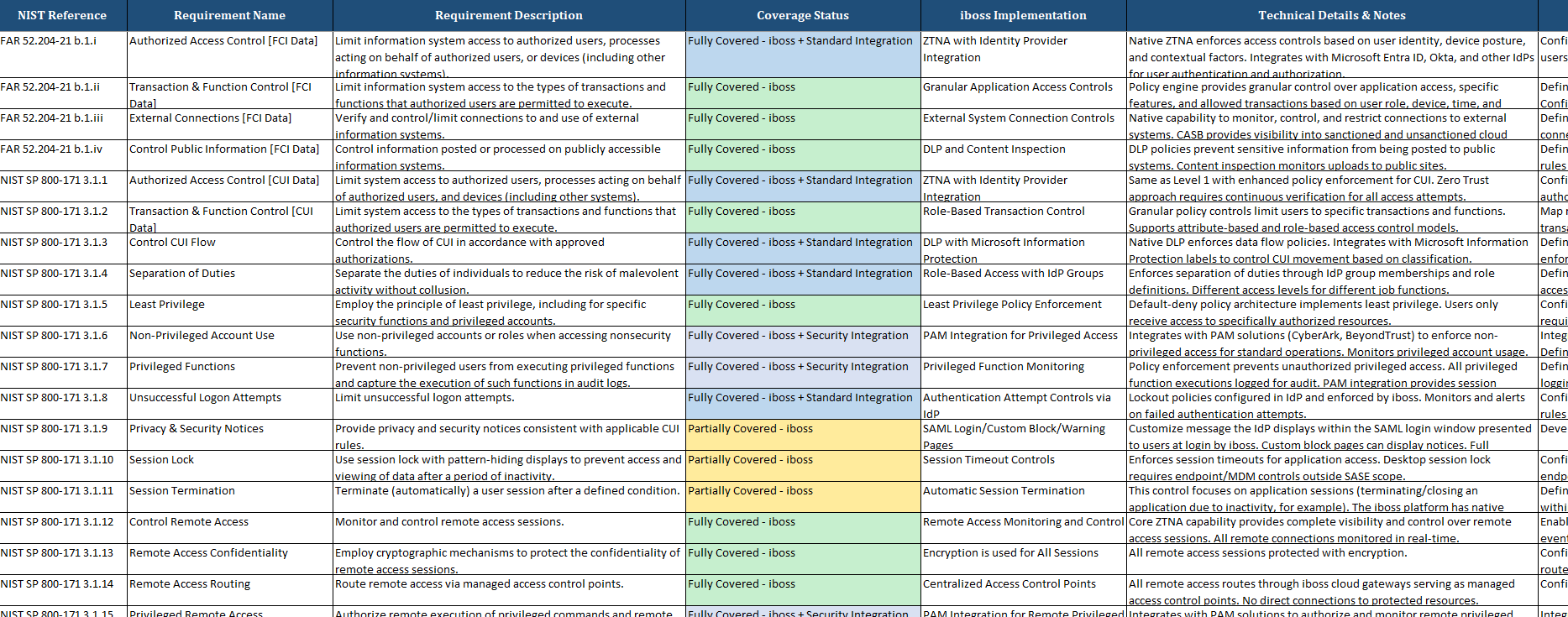
NIST 800-171 Control Family Mapping
See how iboss Zero Trust SASE maps to the NIST SP 800-171 control families required for CMMC Level 2 certification
Access Control (AC)
AC-1 through AC-22
Limit access to systems, processes, and information to authorized users
Audit & Accountability (AU)
AU-1 through AU-12
Create, protect, and retain system audit records
Configuration Management (CM)
CM-1 through CM-11
Establish and maintain configuration baselines
Identification & Authentication (IA)
IA-1 through IA-11
Identify and authenticate users and devices
System & Communications Protection (SC)
SC-1 through SC-44
Monitor, control, and protect communications
System & Information Integrity (SI)
SI-1 through SI-16
Identify and manage information system flaws
CMMC Solutions for Every Organization
Whether you're a prime contractor, subcontractor, or MSP serving the defense industrial base
Defense Industrial Base (DIB) Contractors
Prime contractors and subcontractors in the defense supply chain who must achieve CMMC certification to bid on and retain DoD contracts.
Key Needs:
- CMMC Level 2 certification for CUI handling
- Evidence collection for C3PAO assessments
- Continuous monitoring for ongoing compliance
- Cost-effective security infrastructure
MSPs & MSSPs Serving Federal Contractors
Managed service providers helping defense contractors achieve and maintain CMMC compliance with scalable security solutions.
Key Needs:
- FedRAMP-authorized platform for federal clients
- Multi-tenant management for contractor portfolios
- White-label compliance reporting
- Pooled licensing for cost efficiency
Small Business Defense Contractors
Small businesses in the defense supply chain that need affordable, manageable paths to CMMC compliance without enterprise-scale resources.
Key Needs:
- Simplified security deployment
- Affordable per-user pricing
- No hardware or infrastructure requirements
- Expert support for compliance gaps
CMMC 2.0 Control Mapping Analysis
See exactly how the iboss SASE platform maps to all 125 CMMC controls across 14 security domains. Our comprehensive analysis shows 54% of controls fully covered through technology, with 100% coverage of all technology-applicable controls.
Frequently Asked Questions About CMMC
Get answers to common questions about CMMC 2.0 compliance and certification