SaaS Misconfigurations Are The New Blind Spot: How AI-Driven SSPM Closes The Gap
SaaS Misconfigurations Are The New Blind Spot: How AI-Driven SSPM Closes The Gap
Software as a service has quietly become the system of record for most organizations. Email, files, collaboration, CRM, HR, finance—even classroom content in K-12—all live in platforms like Microsoft 365, Google Workspace, Box, and Salesforce. Data that once sat behind data center firewalls is now distributed across dozens of SaaS tenants, administered by different teams, and constantly changing as users, apps, and integrations are added.
Network and security teams have done the hard work of modernizing access. VPNs are being replaced with Zero Trust Network Access (ZTNA). Secure web gateway controls have moved to the cloud for consistent protection anywhere users connect. Yet one major gap remains:
What is actually happening inside those SaaS applications, and how exposed are they due to misconfigurations and risky settings that no one is actively watching?
Relying only on the native admin console for each app, or periodic audits, is no longer enough. This is where AI-powered SaaS Security Posture Management (SSPM) from iboss comes in.
The Hidden Risk Inside Everyday SaaS Apps
Most organizations assume that if access to SaaS apps is controlled and traffic is inspected, the environment is reasonably secure. In practice, the biggest SaaS risks are not at the network layer at all. They are inside the app:
- Overly broad sharing on files and folders
- External users granted more access than intended
- Legacy accounts that still have powerful roles
- Inconsistent security configurations across tenants
- Third-party integrations with far more permissions than they need
Security and IT leaders know these issues exist. The challenge is scale and complexity.
Each major SaaS platform exposes thousands of settings, toggles, and role definitions. Those settings change over time as new features are released, departments request exceptions, and administrators make one-off changes to satisfy business needs. A well-intentioned configuration for a project can quietly turn into an organization-wide data exposure issue if no one is watching.
Why Traditional Approaches Fall Short
Most teams rely on one or more of the following approaches:
1. Native Admin Consoles
Each SaaS app has its own console with its own language, layout, and reporting. Admins might get good at one platform, but struggle to maintain expert-level familiarity across all of them. There is no unified picture of risk across apps, no way to see recurring patterns, and no shared scoring model that executives can understand.
2. Periodic Audits and Point-in-Time Reports
Security teams or consultants export settings, run scripts, and deliver findings in spreadsheets or PDFs. Those reports might be useful for a short window, but configurations can change days or even hours later. The result is a false sense of confidence, because the documented posture quickly becomes out of date.
3. Manual Scripting and One-Off Checks
Highly skilled engineers attempt to work around console limitations with custom scripts or API calls. While this can surface specific issues, these efforts are difficult to maintain, do not scale well, and often depend on a small number of individuals. When those individuals move on or priorities shift, coverage degrades.
The Business Impact: Cost, Exposure, and Uncertainty
These realities produce three major impacts that both technical and financial leaders care about:
Fragmented Visibility
With each SaaS app managed in isolation, it is almost impossible to answer basic questions:
- Where are the biggest SaaS risks across the enterprise right now?
- Are certain misconfigurations repeating across different apps or business units?
- How does SaaS posture compare to other areas of cyber risk?
Without a unified view, there is no consistent way to prioritize work or demonstrate progress to executives, boards, or regulators.
High Operational Cost
Senior engineers spend valuable time exporting data, writing scripts, resolving discrepancies, and updating manual trackers. That is expensive effort spent on low-level tasks rather than strategic improvements like Zero Trust adoption, incident response tuning, and automation.
Unpredictable Breach and Compliance Impact
When SaaS misconfigurations go unnoticed, the consequences can be severe:
- Accidental exposure of sensitive documents to public or external audiences
- Unauthorized third-party access to customer or student data
- Violations of internal policies or regulatory mandates
- Incident response engagements and potential legal or brand implications
Closing this gap requires continuous, intelligent analysis that understands SaaS platforms at scale and turns configuration data into clear actions.
AI-Powered SSPM Within The iboss Zero Trust SASE Platform
SSPM from iboss extends the value of the existing Zero Trust SASE platform into the SaaS layer itself.
Instead of relying on standalone tools or custom scripts, iboss connects directly to supported SaaS platforms via API through the iboss Integration Marketplace. Once connected, the platform continuously pulls configuration, permission, and security-relevant metadata and analyzes it using AI models tuned for SaaS environments.
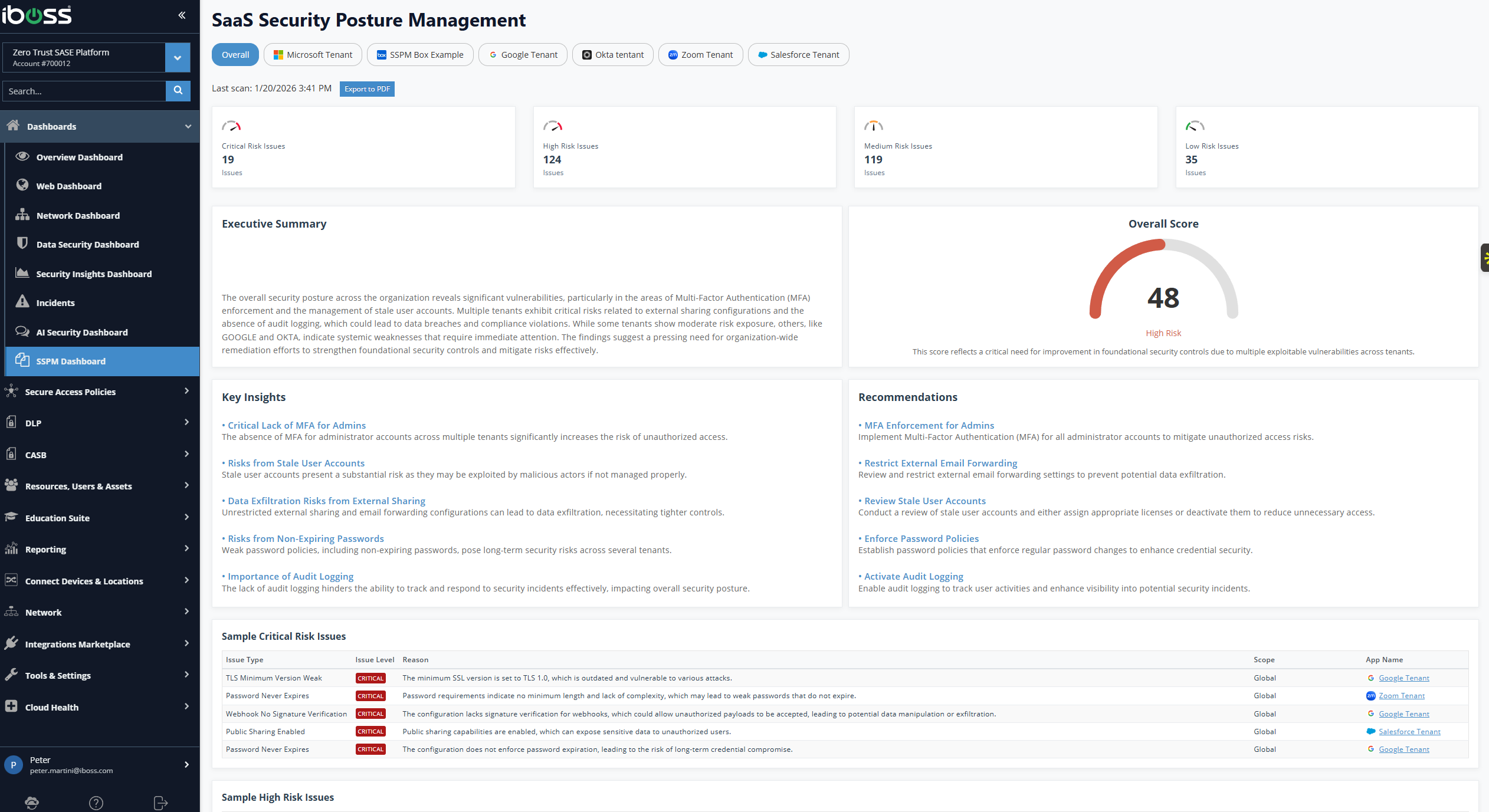
The goal is not just to list configuration issues. It is to provide expert-level insights, clear posture scores, and practical recommendations that teams can act on quickly.
Key capabilities include:
- Simple, agentless connections to apps like Microsoft 365, Google Workspace, Box, Salesforce, and others
- Continuous API scanning so risk visibility stays current even as admins, features, and third-party integrations change
- AI-driven analysis that understands complex relationships between settings, permissions, and data exposure
- Unified posture scoring that summarizes risk across all connected apps in a way that both engineers and executives can interpret
- Application-specific dashboards for deep dives into each platform with detailed evidence and remediation workflows
Because SSPM is delivered from the same platform that already enforces secure internet access, ZTNA, DLP, and CASB policies, organizations gain one place to align SaaS posture with overall Zero Trust strategy.
How It Works: From Connection to Actionable Insight
The operational flow is intentionally straightforward, so teams can move from setup to value quickly.
1. Connect SaaS Apps Through The iboss Integration Marketplace
Administrators select the desired SaaS application and follow a guided process to authorize API access. There are no agents to deploy, no additional appliances to manage, and no changes required on user devices.
2. Continuous API-Based Scanning
Once connected, iboss begins pulling configuration and security-relevant metadata on an ongoing basis:
- Tenant-level security and sharing settings
- Role and permission assignments
- External sharing and guest access patterns
- Third-party integrations and their granted scopes
3. AI-Driven Analysis with Expert Context
The incoming configuration data is processed by AI engines designed to interpret SaaS environments. Rather than simply checking if a setting is on or off, the analysis considers context and relationships:
- Is a permissive sharing policy limited to a specific controlled group, or is it applied broadly?
- Does a third-party integration have privileges that far exceed its intended function?
- Are multiple configuration choices combining in a way that increases data exposure risk?
4. Unified SSPM Insight Overview Dashboard
Findings from all connected apps roll into the SSPM Insight Overview dashboard, including:
- A consolidated posture score that reflects overall SaaS risk
- Clear explanations describing what is driving that score
- A prioritized list of insights and recommendations
- Evidence items that back each finding
5. Application-Specific Dashboards for Deep Dives
Each connected SaaS application receives its own detailed dashboard with:
- An app-specific posture score
- Insights tailored to that platform's configuration and usage patterns
- Recommended actions with associated evidence
6. Guided Remediation Workflows
Within both overview and app-specific views, teams can:
- Assign findings to owners
- Mark issues as in progress, resolved, or accepted
- Track the lifecycle of each configuration change
Why Aligning SSPM With SASE Matters
There are clear advantages when SSPM is part of a unified Zero Trust SASE platform like iboss:
Consistent Policy and Context
The same identities, groups, and device context used for ZTNA and secure web gateway controls are available to inform SaaS posture decisions.
Simplified Operations
IT, security, and network teams already rely on the iboss console for internet and private access controls. Adding SSPM capabilities within that same environment reduces training overhead and avoids yet another console to manage.
Stronger, More Connected Reporting
When SSPM, SWG, ZTNA, CASB, and DLP data all live in the same platform, it is easier to answer cross-domain questions, such as:
- Are risky SaaS sharing patterns aligned with or contradicting our Zero Trust segmentation strategy?
- Do we need to adjust DLP and access policies based on new SSPM findings?
Benefits For Different Stakeholders
For CIOs and CISOs
- A quantifiable SaaS posture score to share with leadership and boards
- Confidence that major SaaS platforms are continuously assessed
- A path to align SaaS risk management with broader Zero Trust goals
For IT, Security, and Network Teams
- A single pane of glass to understand configuration risk across multiple SaaS tenants
- AI-powered insights that reduce manual analysis effort
- Remediation workflows that close the loop between discovery and resolution
For Finance Leaders
- Reduced cyber risk exposure and more predictable security posture
- Lower operational costs from automated posture assessment
- Clear ROI from consolidating SaaS security into the existing SASE platform
See AI-Powered SSPM in Action
Watch how iboss SSPM detects misconfigurations, surfaces actionable insights, and helps security teams remediate SaaS risks:
Getting Started with AI-Powered SSPM
Organizations already using the iboss Zero Trust SASE platform can enable SSPM capabilities directly from the Integration Marketplace. For organizations evaluating iboss, SSPM represents another reason to consolidate security and networking on a platform built for modern, SaaS-first environments.
The gap between access control and application configuration is real. AI-powered SSPM closes it.
Learn more about SaaS Security Posture Management and how continuous posture assessment, AI-driven insights, and unified reporting can transform your security strategy.
Ready to secure your SaaS applications?