Introducing iboss AI-Powered CASB: Signatureless Protection From the Network to the App
Introducing iboss AI-Powered CASB: Signatureless Protection From the Network to the App
Today at RSA Conference 2026, we're launching the iboss AI-Powered CASB — and it represents the most significant advancement in cloud application security since the original CASB was invented.
I'm not saying that lightly. The CASB has been one of the most important security technologies of the last decade. It gave enterprises the visibility and control they needed as their workforces moved to cloud applications. But the CASB was designed for a specific world — one where cloud applications were built by companies, cataloged by vendors, and controlled through API integrations.
That world is gone.
The era of the app catalog is over
Last week, we wrote about the Vibe Code crisis and why the fundamental assumptions behind legacy CASB architecture are breaking down. The response from security leaders confirmed what we've been seeing: the explosion of AI-generated applications has created a data loss surface area that no catalog-based approach can contain.
Here's what's changed: anyone with a browser can now use AI coding tools — Cursor, Replit, Bolt, Lovable, and dozens more — to build and deploy fully functional cloud applications in minutes. These apps have file uploads, form inputs, data sharing, authentication, and every other feature needed to become a path for sensitive data to leave the enterprise. They're deployed to public URLs instantly. And not a single one exists in any legacy CASB vendor's application database.
The security model that depends on knowing about an application before it can be controlled is fundamentally broken. We built the iboss AI-Powered CASB to replace it.
A fundamentally different approach to cloud app security
The iboss AI-Powered CASB eliminates the dependencies that have limited legacy CASB solutions: no fixed application database, no signature updates, no API integrations required. Instead, it uses real-time DOM inspection and manipulation to discover, risk-score, and enforce granular in-app controls on any web application — including applications that were created seconds ago.
This is what we mean by "from the network to the app." iboss doesn't just inspect traffic at the network level and make allow/block decisions. The iboss Cloud Connector agent runs on the endpoint with full visibility into browser activity, reads the fully-rendered page content of any web application, identifies every interactive element — file upload fields, form inputs, share buttons, login forms, text areas, comment sections — and dynamically controls them in real time based on centralized security policies.
The enforcement works on any web application. It works on TypeScript and framework-based applications that require full client-side rendering to reveal their interactive elements. It works on apps that were vibe-coded into existence thirty seconds ago. And it works without any manual onboarding, pre-configuration, or prior knowledge of the application.
How it works: The four-step enforcement model
When a user navigates to any web application — whether it's Microsoft 365, a newly discovered SaaS tool, or a vibe-coded file-sharing app that went live this morning — the iboss AI-Powered CASB executes a four-step enforcement model:
Step 1: DOM Inspection. The iboss Cloud Connector inspects the page's live rendered content, including all interactive elements: buttons, input fields, file upload controls, sharing dialogs, login forms, and more. This is not a static scan of the HTML source — it reads the fully-rendered DOM, which means it works on modern single-page applications built with React, Vue, Angular, or any other framework.
Step 2: Policy Matching. The iboss engine evaluates which CASB policies apply to the current context based on source criteria (which user, which group, which IP) and destination criteria (which domain, which app category, which resource). Policies are created and managed centrally in the iboss cloud console.
Step 3: Real-Time Enforcement. The matched policy controls are applied immediately. The Cloud Connector dynamically modifies the page to enforce the security policy — disabling buttons, making fields read-only, blocking upload controls, removing share functionality. The user sees a clear, customizable browser notification explaining what was blocked and why.
Step 4: Continuous Re-evaluation. This step is critical and often overlooked. Modern web applications are single-page apps that dynamically load new content without full page reloads. As the page updates, iboss continuously re-evaluates and re-applies controls in real time. An app that loads a file upload field asynchronously three seconds after the initial page load is still controlled — iboss doesn't miss it.
The result: any web application, controlled at the element level, in real time, with no prior knowledge required.
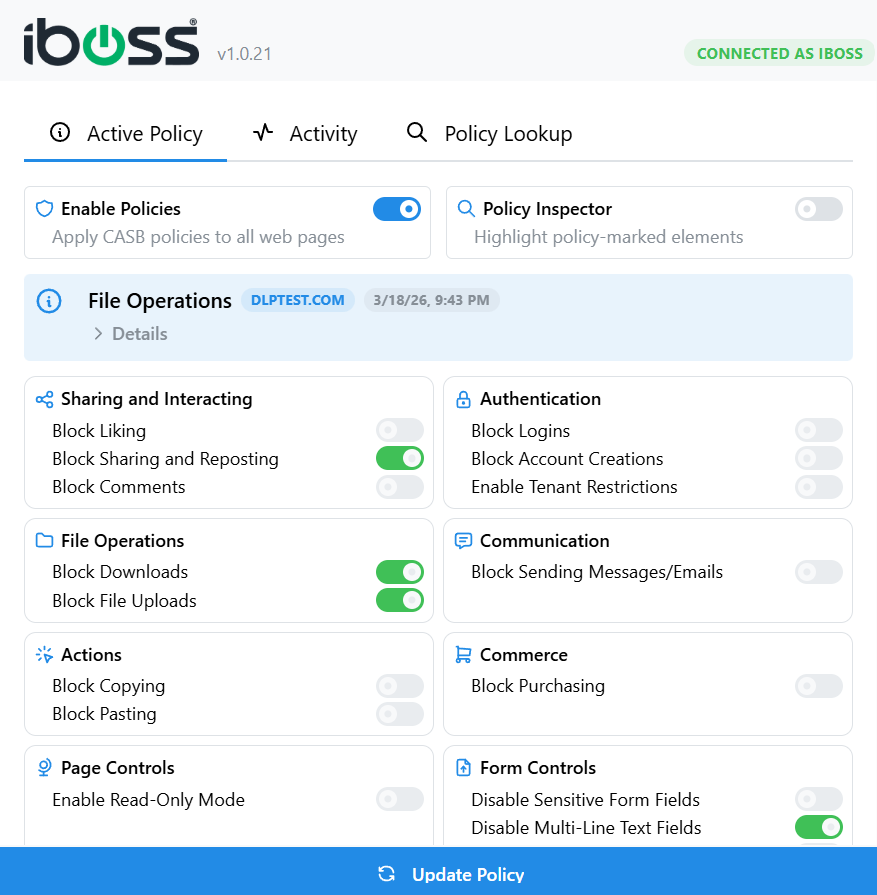
Eight categories of granular control
The iboss AI-Powered CASB provides eight categories of in-app controls, each corresponding to specific DOM elements that the Cloud Connector identifies and manipulates:
File Operations — Block downloads and file uploads. When a user attempts to upload a file to any cloud application, iboss intercepts the upload action at the DOM level and blocks it before any data leaves the device.
Authentication — Block logins, block account creation, and enforce tenant restrictions. The tenant restriction capability is particularly powerful: iboss detects login forms on any application and ensures only usernames with approved organizational domains can authenticate. This works on any app with a login form — no API integration needed.
Sharing and Interaction — Block liking, sharing, reposting, and comments across any web application. iboss identifies social interaction controls in the DOM and disables them per policy.
Communication — Block sending messages or emails within web applications, preventing outbound data exfiltration through in-app messaging.
Actions — Block copying, pasting, and attaching. The paste-blocking capability is especially important for preventing users from pasting sensitive data into AI chat interfaces, vibe-coded apps, and code editors.
Commerce — Block purchasing and checkout actions, preventing unauthorized procurement.
Page Controls — Enable Read-Only Mode, which blocks all interactive inputs on a page simultaneously with a single control. This is the "broad protection" option for unknown or high-risk applications — the user can view content but cannot interact with any element on the page.
Form Controls — Disable sensitive form fields, multi-line text areas (critical for blocking AI prompt inputs and code editors), and all text fields. These controls provide targeted protection against data entry into specific types of fields.
Every one of these controls works on any web application. The application doesn't need to be in a database. iboss doesn't need an API integration. The controls are enforced based on what iboss finds in the live DOM at runtime.
Vibe Code protection in practice
To make this concrete, here's what the iboss AI-Powered CASB does when it encounters different types of applications:
A vibe-coded file-sharing app that was built on Replit thirty minutes ago and deployed to a public URL: iboss inspects the rendered page, identifies the file upload control, and disables it based on the CASB policy. The user sees a notification: "File uploads are not allowed on this app due to company policies." The app was never in any database. iboss never saw it before. It's controlled from the first visit.
An enterprise cloud storage platform like Google Drive: iboss identifies the upload menu, the sharing dialogs, and the file download controls, and enforces granular policies — perhaps allowing viewing but blocking uploads and sharing for certain user groups.
An unknown web tool that a user found through a search — say, an online HTML-to-text converter: iboss applies Read-Only Mode, identifying all input fields through live DOM inspection and disabling them. No prior configuration of this specific tool was required. The security team never had to evaluate or catalog this application.
A developer tool like GitHub: iboss detects the login form and enforces tenant restrictions, blocking attempts to sign in with personal or non-corporate email addresses. The user sees a notification instructing them to use their company credentials.
This is the fundamental difference between iboss and legacy CASB. Legacy CASB controls the applications it knows about. iboss controls any application.
GenAI security: Every conversation captured and protected
The AI-Powered CASB also delivers comprehensive GenAI security — complete monitoring, recording, and DLP enforcement across every major AI platform.
iboss provides full conversation capture across ChatGPT, Microsoft Copilot, Google Gemini, Grok, Anthropic Claude, and emerging AI services. Every question asked and every response received is logged with user attribution, creating a complete audit trail of AI interaction across the enterprise.
Real-time DLP enforcement prevents sensitive data from reaching AI platforms before transmission. Source code, customer data, PII, financial information, and intellectual property are detected and blocked in real time — not after the data has already been shared with an AI model.
Shadow AI discovery uses the same signatureless approach to identify all AI services in use across the enterprise, including tools adopted without IT approval and AI capabilities embedded within existing applications. When a productivity tool quietly adds an AI assistant that sends prompts to a cloud LLM, iboss detects the new data pathway.
Granular policy controls allow per-user, per-group, and per-department rules for AI access and data sharing, with automatic incident creation and full audit trails.
Unified signal intelligence: Why architecture matters
The iboss AI-Powered CASB isn't a standalone product — it's natively integrated into the iboss AI-Powered SASE platform, sharing the same AI engine, policy framework, and data lake as every other security service.
This matters because security signals from inline traffic inspection, out-of-band API analysis (via SSPM), and endpoint telemetry all feed a single AI engine. The result is cross-domain intelligence that fragmented point products structurally cannot provide. When iboss detects that a user is uploading sensitive data to a vibe-coded app through CASB enforcement AND simultaneously has SSPM findings showing misconfigured sharing permissions in their Microsoft 365 account AND endpoint telemetry shows the user recently installed an unauthorized browser extension — those signals correlate automatically.
This is what we mean when we say AI isn't our feature — it's our architecture. The AI engine is the platform. Every signal feeds it, every service benefits from it.
See it live at RSA
We're demonstrating the iboss AI-Powered CASB live at RSA Conference 2026 this week. At Booth 6359, we'll be building applications using AI in real time and showing iboss discovering, risk-scoring, and controlling them within seconds — disabling file uploads, making fields read-only, enforcing tenant restrictions — all with no prior knowledge of the app.
We're doing this because we believe the proof point that matters in 2026 isn't a slide deck or a Gartner position — it's a live demonstration. Build any app. Visit it with iboss. Watch it get controlled instantly.
If your current CASB vendor can do the same, let them show you. If they can't — come see us at Booth 6359.
Learn more about the iboss AI-Powered CASB →
iboss was recently recognized as a Leader and Outperformer in the GigaOm Radar Report for SASE, with the report citing iboss's AI-native architecture — described as "embedded from inception" — as a key differentiator. iboss is rated 4.8 out of 5.0 on Gartner Peer Insights for Security Service Edge.