iboss named a Leader in the 2026 GigaOm Radar for SASEGet the Report →
|🏆IDC MarketScape ZTNA LeaderLearn More →
The
AI-Powered SASE
Platform
iboss ingests deep signals across endpoint, network, and content. Built-in AI surfaces the insights and answers that security, networking, data protection, and executive teams need most.
See the platform in action
AI Chat Monitoring & Security
Comprehensive access controls and monitoring for enterprise AI interactions. Prevent sensitive data leakage while enforcing approved AI tool usage.
Control & Monitor Enterprise AI Tools
AI Access Controls & Monitoring
Control access to AI chat applications and monitor approved enterprise AI tools with comprehensive conversation tracking.
Real-Time Data Loss Prevention
Instantly block attempts to upload sensitive data through AI chats and create security incidents for immediate response.
Enterprise AI Governance
Enforce approved AI tool usage and maintain visibility into enterprise AI interactions through centralized security controls.
Data Loss Prevention for AI Chats
Content Analysis
Scan all uploaded content for sensitive data patterns including PII, financial data, and proprietary information.
Instant Blocking
Immediately prevent sensitive data uploads to AI platforms and notify users of policy violations.
Incident Creation
Automatically generate security incidents for review and compliance reporting when violations occur.
iboss Zero Trust SASE Platform
Every iboss module turns raw activity into actionable insights that answer the security, networking, and executive questions that matter most.
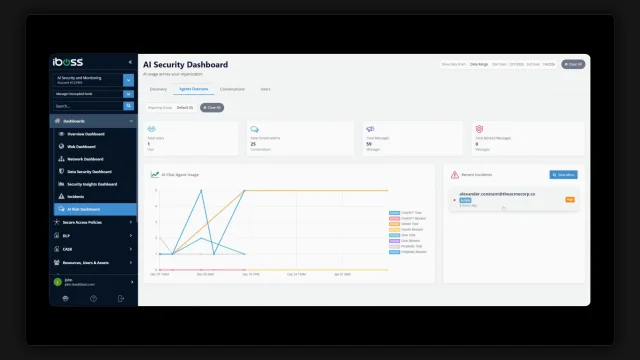
AI-Powered CASB – Cloud app & data signals
Blocks risky SaaS behaviors in real-time while surfacing shadow app usage so teams can take action with confidence.
Learn MoreAdvanced DLP – Content flow intelligence
Prevents sensitive data exfiltration while highlighting data movement patterns that need attention.
Learn MoreSecure Web Gateway – Full session telemetry
Enforces web policies and blocks threats in real-time, with full session visibility for rapid investigation.
Learn MoreZero Trust Access – Identity, device & posture context
Continuously validates identity and device posture before granting access, flagging deviations for review.
Learn MoreBrowser Isolation – Rendered session metadata
Executes risky web content in the cloud while providing session insights for threat investigation.
Learn MoreZero Trust SD-WAN – Branch & edge performance signals
Optimizes network routing in real-time while surfacing performance anomalies that need attention.
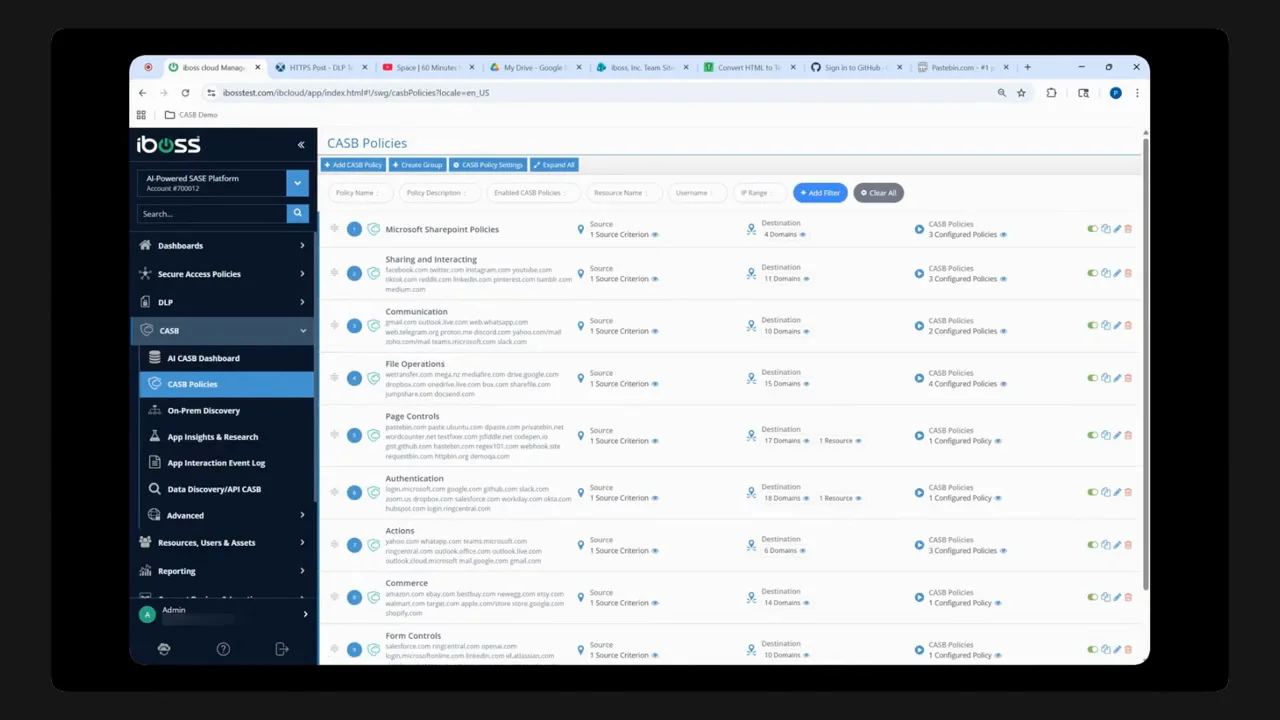
Learn MoreAI-Powered CASB: Security for the Vibe Code Era
Legacy CASBs rely on fixed app catalogs and API integrations — they can't protect against apps that didn't exist five minutes ago. iboss AI-Powered CASB uses signatureless detection and real-time DOM-level control to secure every application, including vibe-coded apps built in seconds.
Revolutionary Dual-Risk Scoring Technology
Unlike legacy CASB solutions that only provide app confidence scores, iboss delivers separate risk assessments for application legitimacy and data loss potential.
Legacy CASB Limitations
Traditional CASB solutions rely on fixed-size cloud app databases and only provide app confidence scores that assess company legitimacy, missing critical data loss risks.
Next-Gen AI CASB
Our AI-powered solution uses signatureless detection to identify data uploads to any application, including zero-day apps not in traditional databases.
Dual-Risk Assessment
Separate scoring for app risk (legitimacy, compliance) and data risk (potential for data loss within your organization).
Interactive Risk Score Visualization
AI automatically detects and scores both application risk and data risk for any app without reliance on a fixed size app database providing immediate insights for data security teams.
Signatureless Detection Technology
Our revolutionary AI doesn't rely on predefined application signatures or fixed databases. It intelligently identifies data uploads and form submissions across any cloud application.
AI-Powered Detection
Machine learning algorithms analyze traffic patterns to identify data uploads and form submissions without relying on application signatures or APIs.
Zero-Day App Protection
Protects against data uploads to brand new applications that haven't been catalogued in traditional CASB databases, including emerging shadow IT.
Deep Visibility
Gain unprecedented insight into file uploads, form submissions, and data movement across your entire cloud application ecosystem.
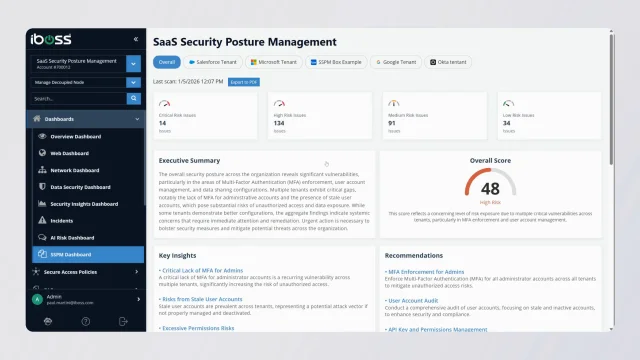
AI-Powered SaaS Security Posture Management
Connect your SaaS applications via API and let AI continuously assess security risks, detect misconfigurations, and provide expert-level recommendations to strengthen your organization's security posture.
- AI-powered misconfiguration detection
- Unified security posture score (0-100)
- Stale account & MFA gap identification
- Actionable remediation recommendations
Data Security Use Cases
See how data security teams use iboss AI CASB to protect sensitive information and maintain compliance across cloud applications.
AI Chat Monitoring
Monitor and record conversations across ChatGPT, Copilot, Gemini, and other AI platforms. Block sensitive data uploads and create security incidents automatically.
Monitor File Uploads
Track and analyze all file uploads across cloud applications to prevent data exfiltration and ensure compliance with data governance policies.
Form Submission Control
Detect and control sensitive data entered into web forms across any cloud application, preventing accidental data disclosure.
Shadow IT Discovery
Automatically discover and assess unknown cloud applications being used by employees, including new and emerging services.
Compliance Monitoring
Ensure GDPR, HIPAA, and other regulatory compliance by monitoring data flows and maintaining audit trails across cloud services.
Incident Response
Rapidly identify and respond to data security incidents with detailed forensics and automated alerting capabilities.
Policy Enforcement
Implement and enforce data loss prevention policies automatically across all cloud applications without manual configuration.
Labeled Content Protection
Prevent transfers of Microsoft Information Protection labeled content over the network, ensuring sensitive documents remain secure across cloud applications.
User Behavior Analytics
Monitor user activities and detect anomalous behavior patterns that could indicate insider threats or compromised accounts.
Transform Your Network Infrastructure
Modernize connectivity with cloud-delivered SD-WAN, Zero Trust access, and unified security that eliminates network complexity while improving performance and security.
Branch Office Connectivity
Connect branch offices with cloud-delivered SD-WAN that provides optimized routing, built-in security, and centralized management.
- Eliminate costly MPLS circuits
- Reduce network complexity
- Improve application performance
- Centralized policy management
Remote Worker Access
Provide secure application access for remote workers without traditional VPNs through identity-based Zero Trust controls.
- Replace legacy VPN infrastructure
- Application-specific access controls
- Device posture verification
- Seamless user experience
Secure Web Gateway
Comprehensive web security with URL filtering, malware protection, SSL decryption, and content control to safeguard users from web-based threats.
- Real-time URL filtering and categorization
- Advanced malware and phishing protection
- SSL/TLS traffic inspection
- Granular policy enforcement
Guest & IoT Access
Secure guest and IoT device access with advanced threat protection, web filtering, and policy enforcement to prevent malicious activity.
- Advanced threat protection
- Web filtering and content control
- Policy-based access controls
- Threat containment and blocking
Ready to Modernize Your Network?
Discover how iboss Zero Trust SASE Platform can transform your network infrastructure with secure, cloud-delivered connectivity solutions.
Unified Microsoft Protection
Seamlessly integrate advanced security capabilities with your Microsoft ecosystem. From Entra SSO to Copilot protection, our Zero Trust SASE platform maximizes your Microsoft investments while delivering unified security across all environments.
Microsoft Entra SSO
Seamless single sign-on integration with Microsoft Entra for streamlined authentication and dynamic policy enforcement based on Azure groups.
- Unified identity management
- Dynamic policy enforcement
- Azure group-based access
- Enhanced security & compliance
Data Label Security
Intercept data transfers and enforce real-time policies using Microsoft Information Protection labels to prevent data leaks and ensure compliance.
- Real-time data loss prevention
- Microsoft MIP label enforcement
- Automated policy compliance
- Enhanced data visibility
Purview Integration
Integrate with Microsoft Purview to inspect and control data transfers in real-time, providing comprehensive visibility and protection.
- Inline data discovery
- Real-time transfer inspection
- Comprehensive data visibility
- Prevent unauthorized transfers
Azure Security Gateways
Extend protection into Azure cloud infrastructure with dedicated security gateways for improved security, reduced latency, and simplified management.
- Azure cloud protection
- Reduced network latency
- Simplified management
- Enhanced security posture
Sentinel Integration
Forward real-time network logs to Microsoft Sentinel for enhanced visibility, faster threat detection, and streamlined compliance reporting.
- Real-time log forwarding
- Enhanced threat visibility
- Faster incident response
- Simplified compliance
Maximize Your Microsoft Investment
Seamless Identity & Access
Integrate with Microsoft Entra SSO for streamlined authentication and dynamic policy enforcement based on Azure groups.
Comprehensive Data Security
Leverage Microsoft MIP labels and Purview integration for real-time data loss prevention and compliance.
Unified Threat Detection
Forward real-time logs to Microsoft Sentinel for enhanced visibility and faster threat response.
Get the Complete Solution Overview
Download our comprehensive Microsoft Solution Suite brief to learn how iboss integrates with your Microsoft ecosystem for unified security and simplified operations.
Next-Gen AI CASB vs Legacy Solutions
See how iboss AI CASB outperforms traditional CASB solutions in protecting your organization's data.
Ready to Transform Your Security Architecture?
Experience the complete iboss Zero Trust SASE Platform and see how our integrated security and networking solution can revolutionize your entire cybersecurity strategy.