Blog
Putting Trust in Zero Trust
Read Morepopular topics:
network security cloud security SASE zero-trust Cloud Adoption Ransomware cloud connector backhaul agent plan Redirect YouTube Google Classroom MDM CASB support policy cybersecurity guidelines NATO REvil Kayesa executive order cyber hygiene objects primitives rules conditions reporting risk dashboard cloud connected inventory count Restricted Mode Allow List override block pages country block file uploads G Suite iOS iPad Safari Chromebook ChromeOS keyword filter Android Always-on VPN Lockdown mode Cloud Access Security Broker block Dropbox block OneDrive block box.com block Google Drive Reports logs event viewer timeframe callout scheduling reports dashboard secure Internet SD-WAN IPSec GRE dedicated IP Microsoft Azure Secured Virtual Hubs Microsoft Virtual Hubs VirtualHubs Internet Security Azure Secured Virtual Hubs SSO migration partners channel RSAC FTP Relay product updates private access cyberattacks EA Sports Data Breach Colonial Pipeline JBS Healthcare HIMSS Microsoft 365 Microsoft partnership reverse proxy API CASB Remote Browser Isolation RBI Cybersecurity Awareness Month cybersecurity awareness Be Cyber Smart FedRAMP ATARC Cybersecurity civil cyber fraud vulnerabilities DLP Data Loss Prevention Cloud App Isolation Exact Data Match Defenders Network Behavior crisis management NIST Apache Log4j Log4Shell Threat Landscape Cyber Threats hackers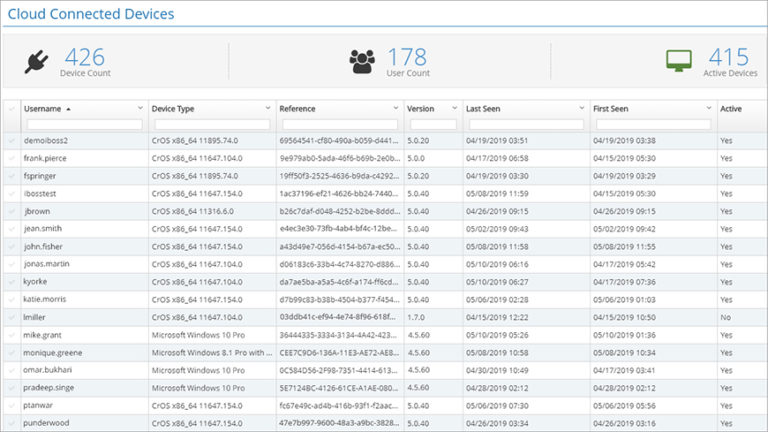
May 16, 2019
Inventory Your Cloud Connected Devices and Revoke Their Internet Access
How do you maintain an inventory of your cloud connected devices when your organization spans multiple states...
count
inventory
cloud connected
May 16, 2019
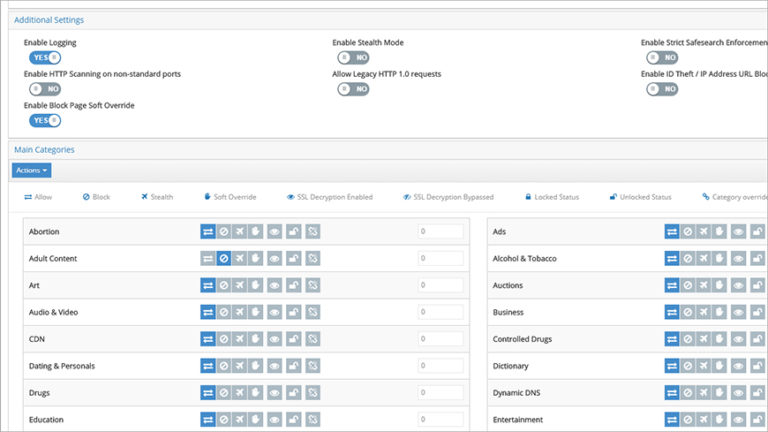
Empower Trusted Users to Override Website Blocks
How do you empower trusted network users to override website blocks independently?
Consider these scenarios:
A user unexpectedly...
block pages
override
May 13, 2019
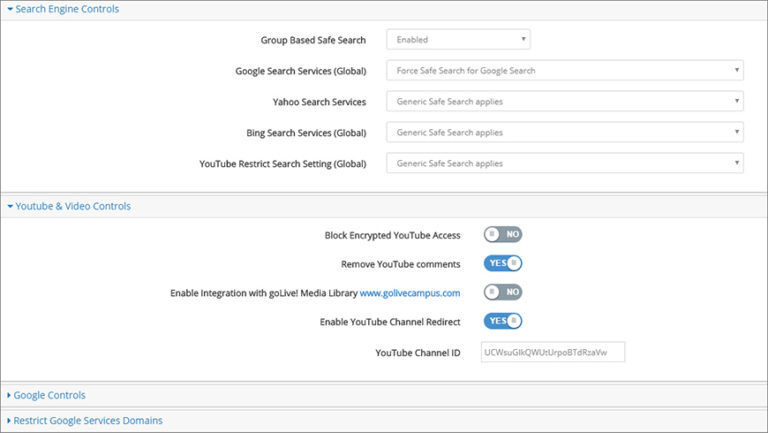
Remove YouTube Comments, Route Users to Your YouTube Channel, and Bypass Restrictions for Individual Videos
Do these YouTube experiences look familiar?
You visit YouTube to locate a specific video, only to be...
Redirect
Allow List
Restricted Mode
YouTube
May 9, 2019
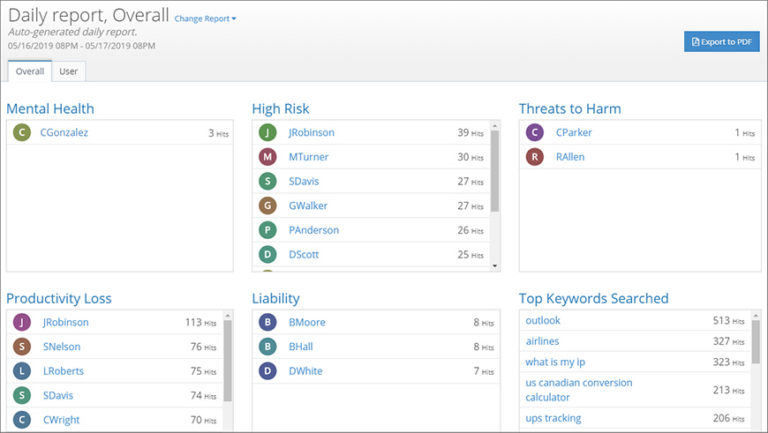
How to Identify High-Risk User Activity and Instantly Generate a Detailed Report
Do these stories look familiar?
You receive an urgent request for a report that details the recent...
risk dashboard
reporting
May 9, 2019
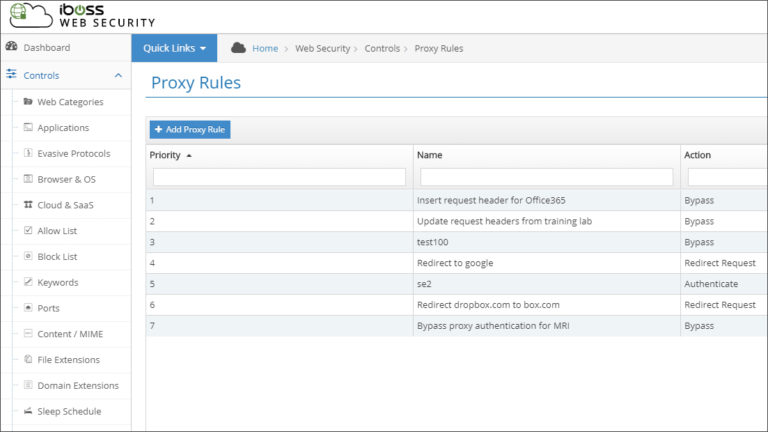
Redirect or Modify User Network Traffic Automatically by Creating Custom Rules
No two networks are exactly alike. This means that you must occasionally find workarounds for challenges and...
Redirect
objects
primitives
rules
conditions



